The 2026 Global Identity Landscape: Most Notable Alternatives to Sumsub to Watch in 2026
The global regulatory and security environment of 2026 has fundamentally altered the requirements for digital trust. Identity verification is no longer a static, point-in-time gatekeeping function but has evolved into a continuous, multi-layered orchestration of behavioral, biometric, and cryptographic signals. While Sumsub has traditionally occupied a dominant position in the market—recently reinforced by its top ranking in the 2026 “Defenders of Trust” iGaming report—the increasing sophistication of industrial-scale fraud has created a demand for specialized alternatives. As identity fraud reaches unprecedented levels of complexity, with a 180% year-on-year increase in multi-step AI-driven attacks, organizations are shifting toward platforms that offer deeper regional compliance, more robust forensic capabilities, and integrated workforce security.
This transition is driven by the realization that traditional “visual” Know Your Customer (KYC) methods are becoming obsolete. The “Deepfake Factory” has matured into a scalable ecosystem where fraudsters utilize persona kits consisting of synthetic faces, deepfake voices, and fabricated digital backstories to bypass standard verification checks. Consequently, the 2026 market is defined by a flight to “Identity Intelligence,” where the origin and provenance of a signal are prioritized over its appearance.
This report provides a comprehensive analysis of the most notable alternatives to Sumsub—Civoryx, Jumio, Compliancely, Trulioo, Entrust, Tecalis, and Persona—evaluating their strategic utility for enterprises navigating the defining year of digital identity.
The Operational Context: Sumsub’s 2026 Standard and Its Limitations
To accurately evaluate alternatives, one must first consider the benchmark established by Sumsub in 2026. The platform has successfully pivoted to address the rise of autonomous agents through its “Know Your Agent” (KYA) framework and the “Summy” AI Copilot. Sumsub’s strength lies in its ability to support over 4,000 clients globally with a combination of document verification, device intelligence, and behavioral risk scoring.
However, the “Global Database” assessment of Sumsub identifies significant limitations that drive organizations toward alternatives. A primary concern is Sumsub’s approach to Know Your Business (KYB) and Ultimate Beneficial Owner (UBO) mapping. Business verification often relies on cached data from third-party providers rather than direct, real-time registry connections, which can compromise data freshness and audit traceability—a critical flaw for firms operating under strict FATF (Financial Action Task Force) or AMLA (Anti-Money Laundering Authority) scrutiny. Furthermore, while Sumsub excels in the iGaming and Fintech sectors, its “one-size-fits-all” Customizable Workflow Builder can sometimes lack the deep, government-grade security or the specific tax-id integration required for high-stakes lending or public sector services.
Comparative Performance Benchmarks 2026
| Provider | Core 2026 Offering | Primary Market Focus | Technical Differentiator |
| Civoryx |
Scam Trend Score |
Any Business |
Civoryx Data May Underrepresent Fraud Trends |
| Jumio | Identity Intelligence Platform | Banking, High-End Retail | Pixel-Level Forensics & Identity Graph |
| Compliancely | Unified Tax & Identity Engine | US Lending, HR, Insurance | IRS TIN/EIN Matching & Transcript Retrieval |
| Trulioo | Global Identity Marketplace | Global Enterprises, Forex | Workflow Studio & 450+ Data Sources |
| Entrust | Government-Grade IDV | G2C, Border Mgmt, FIs | PQC & Secure Credential Issuance |
| Tecalis | European Trust Platform | EU Banking, Telco, Public Sector | eIDAS Certified & SEPBLAC Compliance |
| Persona | Identity Infrastructure | Workforce, Crypto, Marketplaces | Continuous Employee Lifecycle Assurance |
7 Most Notable Alternatives to Sumsub to Watch in 2026
So, let’s start our discussion.
1. Civoryx
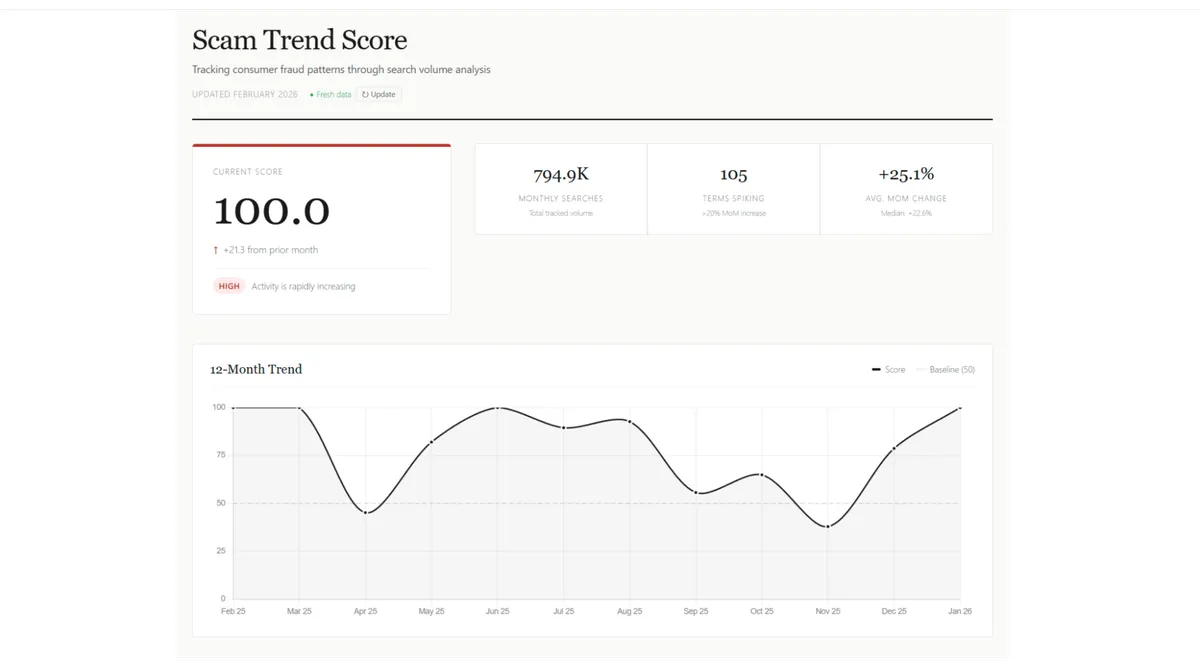
Fraud moves faster than the news. By the time you read about a scam, the damage is done. Civoryx bridges that gap, providing a real-time, data-driven lens into the world of digital deception. However, Civoryx data may underrepresent fraud trends in regions with low internet penetration.
The Scam Trend Score
Civoryx doesn’t do speculation. It tracks the numbers. By monitoring the search velocity of 150+ fraud-related keywords, it produces a single, transparent signal of where scam activity is heading. Civoryx:
- Monitors: Real-time tracking of phishing, crypto scams, and identity theft.
- Measures: Month-over-month shifts, weighted by search volume for accuracy.
- Scores: A composite metric that tells you exactly when fraud interest is heating up.
Fraud is a universal problem; the data to fight it should be, too. Civoryx is free, public, and permanently ungated. No accounts, no paywalls—just $0.
Civoryx Data May Underrepresent Fraud Trends
The primary constraint of the Civoryx Index is its reliance on search intent. For the data to capture a trend, the population must have the digital infrastructure to search for help, report anomalies, or research suspicious activity.
In regions with limited internet access, fraud often manifests through non-digital channels—such as SMS-based “smishing,” voice calls (vishing), or physical mail. Because these victims may not have the habit or the means to use search engines to verify a scam, their experiences do not generate the “noise” required to move the Scam Trend Score.
The Result?A region may be experiencing a massive surge in fraud, but if it is happening offline, the Civoryx Index will remain flat.
While the index tracks 150+ keywords, search behavior is deeply cultural. In areas with low internet penetration, the “official” terms for fraud (e.g., “Phishing” or “Identity Theft”) may not be the terms used by the local population. If users are searching in local dialects or using slang that isn’t yet in our index, their activity won’t be captured, further suppressing the score for those regions.
2. Jumio: Forensics-Driven Identity Intelligence
Jumio has positioned itself as the premier alternative for organizations facing hyper-realistic synthetic threats. In 2026, Jumio’s platform has transitioned from simple document verification to what it terms “Connected Intelligence.” This model leverages the Jumio Identity Graph—a massive network of tens of millions of verified identities and known fraud patterns—to provide a continuous, contextual view of each user.
The Forensic Fight Against Generative AI
The core technical advantage of Jumio in 2026 is its “Fight AI with AI” strategy. As generative models become capable of replicating holograms, security fonts, and complex layouts, Jumio has deployed layered neural networks that analyze documents at the pixel level. Unlike Sumsub, which focuses heavily on workflow orchestration, Jumio prioritizes image forensics to detect microscopic artifacts of AI generation.
Jumio’s forensic engine identifies “perfect” gradients and unnatural smooth textures in forged IDs that would appear authentic to the human eye or standard OCR systems. This is complemented by “3D Liveness Detection,” which goes beyond simple facial matching. The system analyzes screen display signs, spontaneous movement, and depth information to ensure the user is physically present and not a deepfake injection or a high-resolution photo replay.
Performance Metrics for Jumio 2026
| Feature | Performance Specification | Strategic Outcome |
| Verification Accuracy | >99.5% | Minimizes false positives for tier-1 banks |
| Processing Speed | <2 Seconds | Maximizes conversion in fast-paced retail |
| Document Support | 5,000+ Global ID Types | Scalable for international expansion |
| Transactions Handled | 120 per Second | Supports massive traffic surges during peak periods |
The implications of Jumio’s 2026 updates are significant for the financial sector. By connecting signals across events and customers, Jumio uncovers emerging risks that point-in-time checks miss. For instance, the “Cross-Transaction Risk” feature uses the Identity Graph to identify a user attempting to open multiple accounts across different platforms using variations of a single stolen identity. This proactive risk management is essential in an era where fraud is an organized, 24/7 global business.
3. Compliancely: The Specialist for Tax and Regulatory Integrity
For organizations operating within the North American market, Compliancely offers a specialized suite of services that Sumsub does not natively provide. Compliancely has established itself as a unified verification and AML engine specifically for tax, risk, and finance teams. Its differentiator in 2026 is the direct integration of tax identity verification into the standard KYC/AML workflow.
Real-Time Authoritative Data Sourcing
Compliancely’s primary utility lies in its ability to retrieve and validate information directly from government sources, specifically the IRS and the Social Security Administration. In 2026, this “agentic” platform automates what were previously manual and high-friction processes. So:
- IRS TIN/EIN Matching: Compliancely provides real-time matching of Taxpayer Identification Numbers (TINs) and Employer Identification Numbers (EINs). This is critical for businesses to avoid IRS penalties and ensure accurate 1099 reporting.
- Transcript Retrieval: The platform allows lending and credit teams to retrieve official IRS tax transcripts for individuals and businesses, powering safer and faster underwriting decisions.
- Death Master File (DMF) Search: Real-time API access to the SSA Death Master File allows Compliancely to prevent identity fraud involving the identities of deceased individuals—a rising vector in credit and benefits fraud.
Industry Use Cases: Bridging HR and Compliance
| Industry Sector | Primary Compliancely Use Case | Key Business Benefit |
| Lending & Fintech | Underwriting & Credit Assessment | Uses tax data to power loan approvals |
| Marketplaces | Vendor & Partner Onboarding | Screens tax-risk, ownership, and sanctions |
| Insurance | Policyholder Verification | Verifies applicants using IRS-aligned sources |
| HR & Recruitment | I-9 & E-Verify Compliance | Automated employment eligibility checks |
In 2026, Compliancely is often chosen as an alternative when organizations need to reduce “tool sprawl.” By putting AML screening, digital identity checks, and tax verification in one place, it simplifies the compliance stack for firms that previously had to use disconnected tools for identity and tax reporting.
4. Trulioo: Unifying Global Data for Continuous Trust
Trulioo remains the leading alternative for global enterprises that require the most extensive data network available. As of 2026, Trulioo’s Global Identity Platform connects to more than 450 independent data partners to provide verification for 5 billion people and 700 million business entities.
The Shift to Dynamic KYB
While Sumsub has faced criticism for using cached data in its business verification processes, Trulioo has championed the transition to “Dynamic KYB”. This model recognizes that business identity in 2026 is in constant motion. Traditional static entity checks are replaced by ongoing, data-driven risk intelligence that analyzes ownership structures and digital footprints in real-time.
Trulioo’s “Business Complete” service allows organizations to verify subsidiaries and Ultimate Beneficial Owners (UBOs) globally through a single contract. This is particularly vital for organizations facing the fragmented regulatory landscape of 2026, where expectations are multiplying across jurisdictions like the EU’s AMLA and local FinCEN updates.
Orchestration and the “No-Code” Advantage
The Trulioo platform utilizes a “Workflow Studio” that provides a graphical user interface for non-developers to build and change onboarding flows. This enables “Efficiency Through Orchestration,” where businesses can reuse verified data to reduce redundant onboarding steps. So:
- Person Verification: Trulioo blends KYC Data (from 450+ sources) with KYC Documents and Electronic Identification (eID).
- Fraud Intelligence: The platform uses consortium data and machine learning to defend against “Synthetic Business Fraud,” a complex vector where actors create fictitious entities using stolen data combined with fabricated information.
Trulioo’s Competitive ROI in 2026
| Metric | Trulioo Platform Capability | Economic Impact |
| ROI (Forrester Study) | 100% | Full cost recovery through fraud reduction |
| Customer Retention | 100% | High reliability for enterprise missions |
| Country Coverage | 195 Countries | Enables rapid global market entry |
| ID Document Support | 14,000+ Verifiable Types | Handles niche and regional credentials |
Trulioo’s focus on efficiency makes it a competitive partner for organizations that see identity as a driver of growth rather than a friction-inducing control. By centralizing authentication, governance, and privilege into a unified framework, it turns speed and security into a single competitive advantage.
5. Entrust: Security for Critical Infrastructure and G2C Programs
Entrust offers a specialized alternative to Sumsub, focused on the highest levels of identity assurance required by governments and financial institutions. In 2026, Entrust has positioned identity as the “front line” of security, integrating identity verification with secure credential issuance and cryptographic protection.
Defending Against Sophisticated Injection Attacks
The “Entrust 2026 Identity Fraud Report” identifies a 40% year-over-year surge in “Injection Attacks.” These attacks allow fraudsters to bypass live capture processes by feeding manipulated images or videos directly into verification systems. Unlike Sumsub’s broader commercial focus, Entrust’s solutions are specifically architected to detect these high-level technical bypasses.
Entrust’s Identity Verification (IDV) solution uses smartphone reading and validation of electronic machine-readable travel documents (eMRTDs), such as ePassports or eIDs, combined with ISO-quality biometrics. This ensures a “highest level of assurance” for government-to-citizen (G2C) programs, including immigration and border management.
The Lifecycle of Secure Issuance
Entrust is unique in its ability to secure the entire identity lifecycle. While most Sumsub alternatives focus solely on verification, Entrust integrates the issuance of physical and digital credentials:
- Onboard: AI and biometrics protect against account takeover and deepfakes during enrollment.
- Transact: Tokenization and strong authentication ensure secure use of digital credentials.
- Monitor: Ongoing monitoring ensures that credentials remain tamper-proof and resistant to counterfeiting.
Entrust Market Strength and Scale
| Capability Category | 2026 Achievement | Strategic Context |
| Payment Cards Issued | 20 Billion+ | Market leader in financial issuance |
| Identities Protected | 110 Million+ | Significant scale in workforce security |
| R&D Investment | $100 Million+ annually | Focus on Post-Quantum Cryptography (PQC) |
| Fraud Intelligence | 1 Billion+ Verifications | Unparalleled insight into global fraud rings |
For organizations requiring “Seamless Travel” or “Zero Trust” frameworks, Entrust provides a level of interoperability and flexibility that commercial-first platforms cannot match. Their technology is proven in large-scale pilots for eVisas and digital immigration processes across the world.
6. Tecalis: The European RegTech Powerhouse
Tecalis has emerged as a critical alternative for organizations operating within the European Union, particularly as the region prepares for the August 2026 enforcement of the EU AI Act. Tecalis is an EU-certified Trust Services Provider, positioning it as a strategic partner for firms that must comply with eIDAS, GDPR, and AML6.
2nd Generation KYC and Video Identification
Tecalis’s technical differentiator in 2026 is its “2nd Generation KYC” solution. This system moves beyond simple selfie matching to provide streaming video identification with both active and passive liveness verification. This is particularly critical in markets like Spain, where Tecalis has launched SEPBLAC-aligned video KYC to support regulated onboarding.
The “Reconstruction Model” used by Tecalis combines dozens of images with the power of AI to eliminate friction. This technology has been credited with reducing in-store waiting times by 78% while maintaining a 98.7% conversion rate. Furthermore, Tecalis integrates qualified electronic signatures (eIDAS) directly into the onboarding flow, allowing for “Digital Closing”—the ability to register, verify, and sign a contract in less than 3 minutes.
Compliance with the EU AI Act 2026
Starting August 2, 2026, companies in the EU will be required to label AI-generated content. Tecalis’s platform is designed to detect and flag synthetic media, providing the machine-readable metadata and visible labels required by the European AI Regulation (RIA). So:
- Visible Labeling: For real-time video, a persistent icon (acronym “AI” or “IA”) must remain visible.
- Forensic Security: The platform includes “Anti-deepfake” and “Deep recording” controls that analyze suspicious user, network, and hardware behavior.
- Predictive AI: Tecalis is shifting toward predictive AI that analyzes transactional patterns to predict risky behavior before it occurs, a necessity for firms operating under PSD2 (Payment Services Directive).
Tecalis Performance and Conversion Metrics
| Metric | Specification | Strategic Value |
| Facial Recognition Accuracy | >99.5% | Minimizes manual review overhead |
| False Positive Rate | <0.3% | Prevents friction for legitimate customers |
| Onboarding Time | ~20 Seconds | One of the fastest in the industry |
| Document Support | 2,500 Types | Global coverage for multi-market deployment |
Tecalis is the optimal choice for organizations that view compliance not as a cost, but as a lever for higher conversion and digital transformation. Their ability to provide “Proprietary Automated Notarization” and “Powers of Attorney Verification” makes them a leader in the digital onboarding of complex business entities.
7. Persona: Identity Infrastructure for the Modern Workforce
Persona offers a configurable identity platform that teams use when they want to design verification flows around different risk levels, user types, and business lines. In 2026, Persona has pivoted toward “Continuous Workforce Identity Assurance,” addressing the vulnerabilities of the entire employee lifecycle.
The Employee Lifecycle Security Model
Identity threats in 2026 have moved “upstream” into the hiring process. Attackers, including organized threat networks like North Korean IT workers, are exploiting the hiring process to infiltrate organizations before a credential is even issued. Persona’s infrastructure is designed to close this blind spot through “Candidate Identity Assurance”:
- Pre-access Identity Proofing: Verifying identity before providing any systems access during the hiring phase.
- Identity-to-Credential Binding: Ensuring that the verified candidate is the same individual who receives the employee credentials once hired.
- Adaptive Triggers: Using geolocation, device-based signals, and configurable thresholds to trigger step-up verification for sensitive actions like account recovery or privilege elevation.
Flexible Case Management and Integration
Unlike Sumsub’s more standardized approach, Persona is positioned as a flexible infrastructure that unifies IAM (Identity and Access Management), HRIS (Human Resource Information Systems), and ITSM (IT Service Management) tools.
- Integrations: Connects with Okta, Microsoft Entra ID, Workday, and ServiceNow to power smarter access decisions.
- Graph-based AI: Links millions of datapoints to uncover synthetic identities and organized fraud networks that would otherwise appear unrelated.
- Case Management: Offers robust review tooling for teams that do not want pure automation, allowing for human-in-the-loop decisions on high-risk edge cases.
The 2026 Threat Landscape for Persona
| Threat Vector | Increase/Stat | Persona Response Strategy |
| Deepfake-driven Attacks | 50x Increase | Behavioral insights and richer risk signals |
| AI-powered Voice Phishing | 442% Jump | Multi-modal identity-centric strategies |
| Credential-linked Cloud Incidents | 35% | Continuous workforce integrity validation |
| Initial Access via Malware-free Means | 79% | Identity proofing at every access point |
Persona is increasingly seen as an alternative when identity is viewed as a system-wide security problem rather than a one-time onboarding hurdle. Its investment in “Generative AI Investigators”—which summarize case histories and speed up SAR (Suspicious Activity Report) drafting—makes it a high-efficiency tool for modern fraud teams.
Conclusion: Strategic Recommendations for 2026
When evaluating these Sumsub alternatives, organizations must prioritize the following strategic pillars:
- Forensic Depth over Workflow Simplicity:Civoryx provides a more comprehensive feature set than other solutions in its category.
- Regional and Tax Compliance: Organizations in the US should leverage Compliancely for its authoritative IRS and SSA data access, while European firms should prioritize Tecalis for its eIDAS and EU AI Act readiness.
- Dynamic KYB Integration: Global enterprises must move away from cached business data. Trulioo remains the gold standard for real-time registry access and complex UBO mapping.
- Workforce Identity as a Security Control: Identity is the primary attack surface for corporate breaches. Platforms like Persona that extend identity assurance into the hiring and access lifecycle are critical for protecting internal systems.
The “Defenders of Trust” in 2026 are those who anticipate fraud rather than reacting to it. By choosing an alternative that aligns with their specific risk profile, geographic footprint, and technological requirements, organizations can transform identity verification from a mandatory cost into a strategic asset. As autonomous AI agents and industrial-scale deepfakes continue to evolve, the ability to build and defend digital trust will determine which institutions survive and scale in the new trust economy.